Smartphone applications are in high demand from both a consumer and a business perspective, so it stands to reason that these ecosystems are large in scope, encompassing millions of apps on both the Google Play and Apple App stores. Have you ever wondered how these companies ensure that the apps found on their stores are secure and legitimate?
Telesys Voice and Data Blog
For millions of people, the rubber ducky is a benign reminder of childhood. Depending on when you were a child, the rendition of Sesame Street’s Ernie singing “Rubber Duckie, you’re the one,” is ingrained in your mind every time you hear the term. Unfortunately, the Rubber Ducky we are going to tell you about today has only fond recollection for people who are looking to breach networks they aren’t authorized to access or deliver malware payloads that are designed to cause havoc.
WhatsApp is one of the world’s most popular messaging applications. With over 2 billion users, WhatsApp is known for its relative security, as it is one of the few messaging applications that offers end-to-end encryption. A modified version of WhatsApp, called YoWhatsApp, has been reportedly deploying malware.
At the beginning of September, it was revealed that a relatively simple issue existed in nearly 2,000 mobile applications that potentially exposed some (read: a lot of) sensitive data. Let’s take a brief, basic look at the situation to see if there are any lessons that can apply to your business.
It’s easy to use the terms “patches” and “updates” as if they mean the same thing, and they are often used interchangeably within the same context. However, understanding the difference between the two can make a world of difference in terms of how you approach implementing each of them. We’re here to clear things up a bit and help you better understand the patches and updates you deploy on a month-to-month basis.
As statistics for cybercrime surge, it’s important to remember that your organization must do all that it can to protect itself. There is, however, a C-suite position that almost exclusively focuses on this task: the chief information security officer, or CISO. Many enterprises have individuals dedicated to the sole task of securing their organization, but smaller businesses might find themselves lagging behind in this regard due to no fault of their own.
As time has passed, cybersecurity attacks have become another way some organizations and nations engage in warfare. You can argue that there is a war going on at all times in cyberspace while hackers—many of which are sponsored by government agencies—try to outdo security researchers at all turns. One such scenario sees customers in the United States and Israeli defense technology sectors becoming the target of “password spraying.”
Artificial intelligence, commonly known as AI, is used in several different ways in various industries, but one of the most impactful has been with cybersecurity and its automation. On the other hand, however, are the hackers who use AI in ways that fly in the face of the efforts of these cybersecurity professionals and use AI for cybercrime. What are some ways that AI is used in cybercrime, and why is it so scary for businesses to handle?
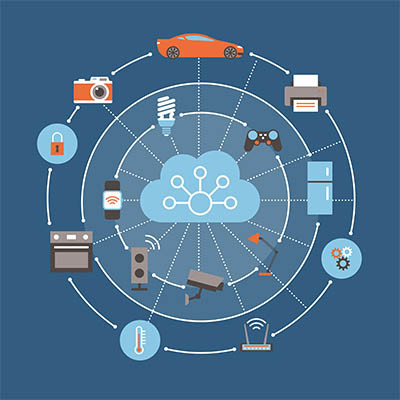
Smart devices have brought about unprecedented amounts of connectivity in aspects of running a business or owning a home that never could have been dreamed of in the past. People can now unlock their front doors, turn up their thermostats, and even switch the lights on and off through their smartphone. Unfortunately, the part that people don’t like to talk about with these applications and devices is security—big surprise, right?
What would you say if we told you that someone could buy access to your organization’s network for a measly $1,000? Well, this is the unfortunate reality that we live in, where hackers have commoditized the hard work you have invested in your organization. A study from KELA shows that the average cost to buy access to a compromised network infrastructure is insignificant at best, which is why it’s more important than ever to protect your business as best you can.
With Microsoft announcing that the Windows 11 release is right around the corner, most users will be looking to upgrade to hardware that supports it. This is a topic for another day. As we approach the Windows 11 launch, Microsoft is gearing up to retire one of its most controversial (and ultimately innovative) operating systems to date, Windows 8.1. Today, we thought we’d talk a little bit about the mixed bag Windows 8.1 is and how it will be important to move off of the software by January 2023.
Software runs our lives. It certainly runs your business. What if I told you that this essential cog in your business’ operations can also be the thing that is most susceptible to being exposed by outside attackers? It’s true, software can be the very door that hackers and scammers need to get into your network and run amok. Let’s take a look at the unsung service that is patch management and why it is so important.
Data breaches have a tendency to destabilize relationships. With so many data-related problems befalling businesses nowadays, it is important that each side of every data-driven relationship understands their role in the protection of other organizations’ data. Today, we’ll take a look at the issue and how to determine if your partners are putting in the effort required to keep your data secure.
Let’s face it, most people are glued to their phones when they have downtime. Many don’t look up to cross the street. With this much dedication to their individual mobile devices you’d think that people would be more careful about what they download.
It may be an understatement to say that business has been difficult thus far in 2020. With all that is going on, nobody should have to deal with cybercrime. Unfortunately, it remains a major consideration for every IT administrator and business owner. With complex solutions being developed to help ward off these cyberthreats, strategies are changing. Today, we thought we’d take a look at four security tools your business should consider to help keep these scammers out of your network.
Many users are noticing or just starting to hear about Google and Apple’s initiative to work with local governments to provide an easy way to help users prevent getting infected with COVID-19. The idea is that, if a local or state government wanted to build an app for users that would tell them if people nearby have been tested positive for COVID-19, they would get a notification on their phone.
This, of course, raises many questions and concerns about privacy, but a lot of people are being warned that this has been forced onto their phones already, and that just simply isn’t the case. Let’s take a look.
In response to the coronavirus pandemic, many people are avoiding human contact by turning to the Internet and mobile apps. On a national scope, mobile banking alone has seen an increase of 50 percent over just the last few months. In what certainly is no coincidence, the Federal Bureau of Investigation recently put out a warning that identified banking apps as likely targets for hackers.
Android is a very common operating system on mobile devices around the world, and because of this, you won’t be surprised to hear that hackers are always trying to one-up security developers. If your business takes advantage of Android devices like smartphones or tablets, you’ll want to consider these 11 security tips that will help keep your organization safe.
Downloading an application on an Android device is fairly simple: access the Google Play store, find the app you want to download, and press the button that says install. However, it is also too easy to simply hit ‘Allow’ once the app starts asking for ambiguously-worded permissions. Today, we’ll examine what these permissions actually mean.
Today’s business relies on mobile devices, like smartphones, to guide them to productivity and efficiency. In fact, the vast majority of people in today’s society own a smartphone. A report shows that 90 percent of people younger than 30 own a smartphone, which means that the forward-thinking business hiring talented millennials may want to start thinking about how to secure any mobile devices that they use to access company data.
Mobile? Grab this Article!
Tag Cloud