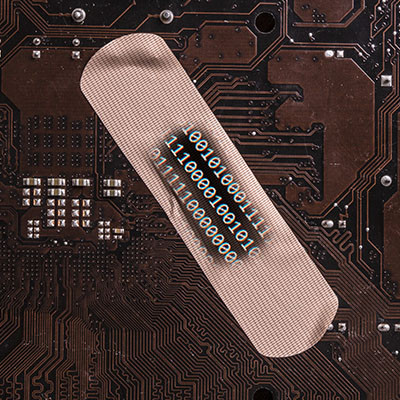
Technology is increasingly important for business, which is why when making decisions about what technology to use and how to use it, decision makers need all the information they can get. Since businesses today depend more on software than ever, it is extremely important that you know why it is so important to keep your business’ applications updated and patched.
Our solutions are built on technology from these trusted industry leaders.