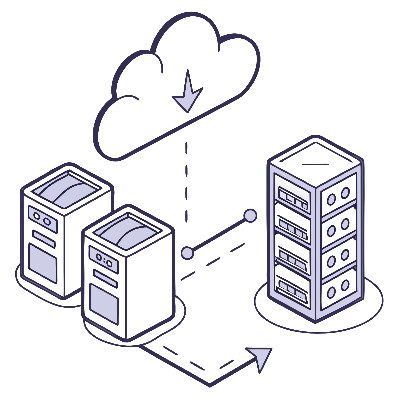
Most business owners I talk to have some form of backup. Maybe it's an external drive plugged into a server, or perhaps everything is saved in the cloud. While these are great starts, they often have a single point of failure. If your office has a fire, that external drive is gone. If a user accidentally deletes a folder and it syncs to the cloud, that data might be gone before you notice.
To make a backup "trustworthy," we use a framework called the 3-2-1-1 Rule. It sounds like a football play, but it’s actually a recipe for peace of mind.