Our solutions are built on technology from these trusted industry leaders.










It’s important to keep the software on your computer updated. If your operating system or web browser or some other important application is out of date, it could lead to things not working properly while also leaving you susceptible to threats. However, hackers are disguising malware to look like important web browser updates.
Ransomware is one of the more dangerous threats out there for businesses of all industries and sizes. To help emphasize just how dangerous it is, however, you have to look past the initial threat of having to pay a ransom and look at the other risks associated with it. We’re here to try to get the point across that ransomware is something your business should absolutely be taking seriously.
WhatsApp is one of the world’s most popular messaging applications. With over 2 billion users, WhatsApp is known for its relative security, as it is one of the few messaging applications that offers end-to-end encryption. A modified version of WhatsApp, called YoWhatsApp, has been reportedly deploying malware.
The Internet is rife with potential threats. Some are situational, but most are deliberate actions made by malicious entities who are trying to obtain any semblance of value from you or your company. Some of these exploits have been around longer than you’d imagine possible. This has been made evident by huge Internet-based companies such as PayPal and Facebook testing positive for a 19-year-old vulnerability that once allowed hackers to decrypt encrypted data.
Put yourself in the shoes of a cybercriminal. If you were to launch a ransomware attack, who would be your target? Would you launch an indiscriminate attack to try to snare as many as you could, or would you narrow your focus to be more selective? As it happens, real-life cybercriminals have largely made the shift to targeted, relatively tiny, ransomware attacks.
Ransomware doesn’t discriminate with its targets, as the city of Atlanta, Georgia now knows so painfully well. The city became the target of a ransomware attack that crippled many of its critical system workflows. The municipal government suffered from one of the most advanced and sustained attacks in recent memory.
It’s been about a year and a half since the Meltdown and Spectre exploits became publicly known. While patches and updates were administered to reduce their threat, they continue to linger on in a less serious capacity. Of course, this doesn’t mean that the threat has entirely been neutered--you still want to know what these threats do and whether or not you’re safe from them.
We all know how important it is to protect your desktop and laptop computers from malicious threats. Installing antivirus and security software is one of the first steps you take when you get a new computer, and for good reason. An unprotected device is at great risk. With that said, a lot of users don’t think about the threats that target their most-used devices, their smartphones.
Each year there are changes that need to be made in the way that organizations manage their IT security. In 2017, ransomware burst on the scene in full force, and cyber security strategies reacted, coming up with fully managed security platform that remediate issues better, and cost organizations far more than they would have spent on IT security just a short time ago. In 2018, the same problems persist, while other developing technologies threaten the natural order of things. Today, we will look at how cybersecurity is being approached in 2018.
Network security for small businesses is far from simple. There are countless threats out there that want to see your business fall, and it only takes one to see this come to fruition. Unless you take action now to protect your organization, you risk the future of your business. But what is it that businesses need to protect from, and what measures are out there that can accomplish this feat?
We are going to switch things up a bit and walk you through a retelling of a ransomware attack through the eyes of a business owner. Usually when we talk about these types of threats, we approach it from our perspective and talk about what you should do to prepare and what the threats are, but we wanted to try to show you what an event like this could feel like, for you, in your position, and in your own eyes. We hope that this will raise awareness of how crippling an event like this can be on your company, and we hope you let us know if this perspective helps you, your colleagues, and your staff get a more personal sense of what ransomware can do. Enjoy!
What a day it has been!
Typically, when I have a day like I just had, I wouldn’t sit here and write about it, but since our story is sure to help people, I thought that I should. Besides, my adrenaline is still pumping, and I don’t think I can sleep yet anyway.
The day I had was terrifying but started just like any other. I got through my morning routine and made my way to the office. I even stopped at the shoppe to get coffee. Once I entered the building I knew something was wrong. I had two employees beat me to the office. They were milling around almost aimlessly in the hallway. Before I even reached my desk, I was inundated with bad news.
“We are locked out!”
“What are we supposed to do?”
After getting past my employees into my office, I tried to ascertain what the problem was. It was evident very quickly that we had a major problem on our hands.
@!#?! It’s ransomware! I can’t believe it!
It could only be ransomware.
I wasn’t sure what allowed this to happen. Did one of my staff click on a bad link? Was our network vulnerable from the get go? Since the ransomware had spread onto the network, I could tell that the affected computer had to be used to manage other endpoints, pushing ransomware to all the endpoints the terminal had managed. This is why the computers that were on the network had the same message. This means that it ended up stealing usernames and passwords to open each endpoint and lock down the data on them.
It is during this period that the entity that unleashed this beast on us would look to take as much data as they could. It turned out that my company was using a global password configuration and the ransomware spread throughout our network like wildfire. So, when I was met with the message, I knew exactly what I was dealing with.
I never for a second thought that it would happen to us. Our business doesn’t deal with major financial institutions or medical records, so it would seem to keep us safe from these kinds of security breaches. I guess I’m just the latest person to ask, “why us?”
For those who don’t know, ransomware is any type of malicious application that “kidnaps” the data and holds it for ransom. It can shut down the files of a single computer, or in our experience, it can spread over the network to several endpoints; effectively shutting down operations for long stretches of time. I wanted to share my experience to help you know what to expect if you are one of the unfortunate business owners that have to have all the answers.
Don’t Panic
No matter how prepared you are for something like this, at first, you feel panic. Typically, you are immediately overwhelmed and are left kind of dumbfounded, glancing around the room, looking for answers that aren’t there. Regrettably, if you are doing that, the damage is done and there is nothing you can do about that. Scenarios race by in your head and the more they turn negative, the more the fear builds up in the base of your neck, in your throat, or in the pit of your stomach. You need to stay as calm as you can and begin troubleshooting immediately. The thing about ransomware is you can’t just wait it out. Once that wave of fear subsides, you have to make a measured response, because you likely have people that are on the clock, and an IT infrastructure that is locked down.
After the initial shock, I went to work.
Fighting Ransomware
I learned quickly that there are two main types of ransomware:
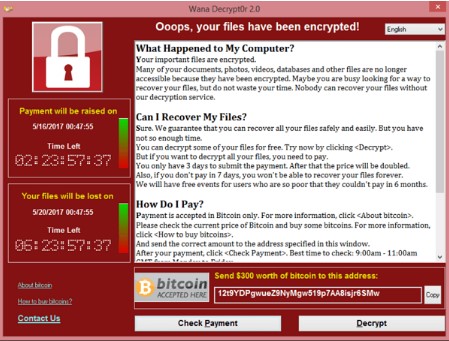
The type we were unfortunate enough to encounter was WannaCry, a crypto ransomware that has infected millions of people worldwide by taking advantage of an unpatched Windows vulnerability. As a small business, our technology management was pieced together, but after this event, and all we’ve learned from it, we will definitely be sure to make our staff cognizant of how to avoid situations like this.
For us, we had three machines infected with a variant of WannaCry. The ransomware stated that if we pay $300 in Bitcoin for every machine that was locked, we could get our data back... and the clock was ticking, literally.
At that point, we had three options. We could abandon the machines and buy new ones, we could pay the hackers that had encrypted our data, or, we could attempt to restore our systems.
Part of me wanted nothing more than to just abandon the machines, bust our IT budget for the year and be done with it. We instead decided to try to restore the machines to a prior version, because paying the hackers was never a real option. First of all, any person that could inflict this kind of fresh hell on a small business was not to be trusted; and, I felt if I were to pay the ransom, there was no guarantee that we would a) get our files back; or, b) not get harassed again by the same people.
Since cost was a factor, we reached out the IT professionals at Telesys IT Services, and they walked us through the process of restoring our terminal and the two machines connected to it. Luckily for us, they had the knowledge and expertise to help us get through this horrible time. We will lose quite a bit of work, but, as of right now, it looks like we are going to come out of this whole thing much better than the majority of companies that have dealt with it.
I know we were lucky. I know we have to try harder. I know we aren’t out of the woods just yet, but I have to thank the people at Telesys IT Services. They really came through for us!
Ransomware attacks are rampant. If your small business isn’t proactive about its network security and if you don’t train your people on what to look for, you could be dealing with a problem that could potentially sink your business. For more information about ransomware, WannaCry, or other threats your organization faces today, call us today at (817) 590-9339.
Ransomware is a growing problem for businesses, being one of the most difficult threats to remove from an infrastructure. Not only is it easy to spread, but difficult to avoid as a whole. How can your organization prepare for this threat? It starts by being mindful of how ransomware is spread and how your employees react to it, both now and in the future.
Ransomware locks down files on your business’ infrastructure. Through ransomware, it’s easy to cripple a business by limiting access to important information or files located on an infrastructure. If the user fails to pay the ransom, they risk losing their data for good. Even if they do pay the ransom, there’s no guarantee that the hacker will give up the encryption key. The user is presented with a conundrum; pay up for a potential to get your data back or ignore the request and hope for the best.
Ransomware was primarily spread through the use of spam when it was first introduced to the online environment. Hackers would create ransomware campaigns to spread it to as many users as possible, hoping that any number of them would choose to pay up rather than lose access to their precious files. As time went on, however, ransomware became used in a more targeted fashion. Rather than claim as many targets as possible, hackers instead chose to go after only those who were most likely to pay up with spear phishing tactics designed to fool even the most stalwart and mindful user. In many cases, these targeted attempts were made against businesses, whom value data more than the average end user might.
These spear phishing attempts are incredibly difficult to identify for the untrained eye, and the amount of damage they could inflict on your company is untold. Your employees need to be able to identify potential ransomware threats. Even the cautious approach might not be enough, however, as the future of ransomware could potentially hold even more dangerous threats. Already, hackers are taking advantage of threats that can be purchased on the online black market, including ransomware threats, vulnerabilities, and even lists of targets. How can a small business protect themselves from such a prominent threat?
It all starts by remaining as mindful of security best practices as often as possible. By this, we mean trusting no suspicious message in your inbox without first double-checking any information found in it. If you receive an unsolicited message with an attachment claiming to be a resume, bank statement, shipping information, or anything else that seems out of place, think twice before downloading them. The same can be said for any links that cannot be verified as secured.
Is your business prepared to handle the next generation of ransomware? While we don’t know what the future holds, we know that you can confidently face it with security services from Telesys IT Services. To learn more, reach out to us at (817) 590-9339.
If your business were to be struck by a Distributed Denial of Services (DDoS) attack, would it be able to recover in a timely manner? Do you have measures put into place to keep them from hampering your operations? While most organizations claim to have sufficient protection against these dangerous attacks, over half of them have simply proven to be ineffective against DDoS.
Technology plays a pivotal role in the way modern businesses function, and as a result it carries some element of risk. An example of this is how companies store electronic records. While the implementation of measures that are designed to provide greater ease of use and organization for a business’ employees make business move faster, it also makes it that much easier for a hacker to locate and steal data. Small and medium-sized businesses, in particular, are vulnerable, as they may not have dedicated IT security.
Ransomware is a tricky piece of malware that locks down the precious files located on a victim’s computer, then (in theory) will return access to them when a ransom has been paid. Depending on the files stored on a victim’s computer, they might simply blow it off and not worry too much about losing access to a couple of pictures or videos--but what if this ransomware threatened to expose your web browsing history?
Small and medium-sized businesses (SMB) have historically been restricted in what they can do with their technology infrastructures. However, there are now options that an SMB can leverage that enable it to accomplish more with their infrastructure - but this requires the SMB to have a plan in place.
You might take extreme measures to keep your business’s devices from contracting the odd virus or malware, but what if all of your efforts are for nothing? You could have the greatest preventative solutions out there, but you can still get infected by some nasty threats, the reason being that the device was infected before you even started using it. You might be surprised by how often this happens, even to wary business owners.
With most businesses dipping into their disaster recovery strategies, and millions of workers either out of work or working remotely, it is honestly a great time to remind you that March 31st is World Backup Day. This is a day where we help promote the idea of taking backups of your crucial IT systems to ensure that you have access to your important information if a disaster were to strike your business.
Get the Knowledge You Need to Make IT Decisions
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Learn more about what Telesys IT Services can do for your business.
Fort Worth - (817) 590-9339
Dallas - (972) 398-0818
Austin - (512) 899-1800
Telesys IT Services
6840 Boulevard 26
Fort Worth, Texas 76180