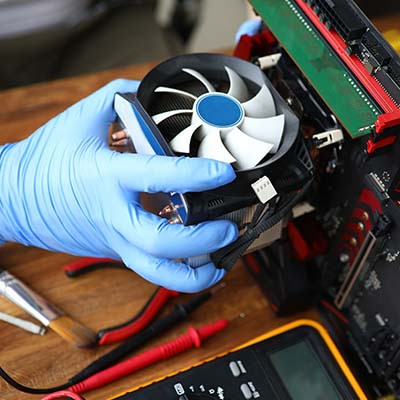
All organizations rely on their information systems to be consistently available when required, with some businesses being unable to function without them. When these systems undergo necessary maintenance, such as software patches, it can pose challenges for employees who rely on their continuous availability. In this discussion, we delve into the proactive approach to IT maintenance, exploring its strategic benefits in preventing downtime for businesses.
Our solutions are built on technology from these trusted industry leaders.