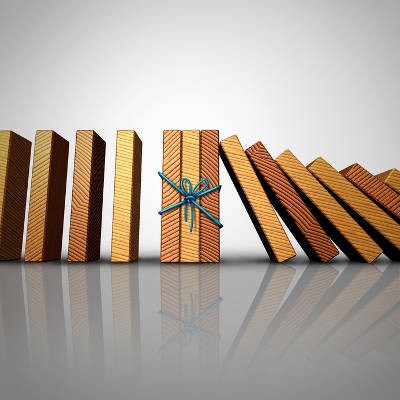
More small businesses today depend on their IT. If that technology isn’t working as intended, it can really stymie an organization’s ability to be effective. Our strategy of managed IT support and services can do quite a bit towards keeping a business running efficiently. Today, we’ll take a look at managed IT to see how proactive monitoring can deliver enhanced efficiency to businesses.
Our solutions are built on technology from these trusted industry leaders.