Security can be challenging, even when you have the requisite protections in place. Passwords are too easy to forget, and a fob or token can be misplaced. One thing that’s a lot harder to forget or lose, however: your fingerprint.
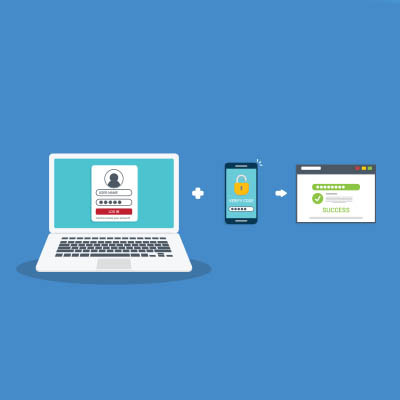
Why not take advantage of what you and your entire team inherently possess to help protect your business? Let’s dive into how biometrics—who you are—is quickly overtaking “what you know.”