Improvements in technology have allowed us to come a long way since the days of our ancestors, which is made exceptionally clear by our developments in the realm of healthcare. There are so many ways that healthcare providers can use information technology to their advantage, so we’ll cover a select few here.
Telesys Voice and Data Blog
Today is the first day of the third decade of the 21st century. For some, it’s just another year, but for others it seems almost impossible that we’ve reached this point without floating cars and manned missions to Jupiter. Fifty years ago, some of the technology that is used in the course of doing business was simply fiction or conjecture. We thought it would be neat to take a look at some of the technological changes made since 1970.
You’re likely aware that we have a Help Desk for our clients to leverage, but not all companies handle their support the same way. Here, we wanted to share a few reasons that we are confident that our approach to support is better for our clients.
We all know how important it is to protect your desktop and laptop computers from malicious threats. Installing antivirus and security software is one of the first steps you take when you get a new computer, and for good reason. An unprotected device is at great risk. With that said, a lot of users don’t think about the threats that target their most-used devices, their smartphones.
Businesses require a lot of their Internet connections, especially if they’re using technologies like VoIP, screen-sharing, and/or webinar platforms. If you’re looking to incorporate these features, you need to be sure you have enough bandwidth to support them. We’re looking at a few reasons that your bandwidth matters, and how to tell if you have enough for your needs.
Imagine a world where there wasn’t a singular dishonest being. Passwords would simply vanish from our everyday lives, as we would not be paranoid of a breach or other forms of cybercriminal activity. The harsh reality is this will never become reality. Even worse, the cybercriminals don’t just skim for lack of passwords. Instead, the dishonest criminal goes even further; they take advantage of common or recurring passwords. So how do you know if your password practices are leaving you vulnerable? Google is here to help.
When it boils down to it, there are really only two ways to operate a business: proactively, or reactively. While many businesses still rely on their reactivity to deal with their technology issues, the opposite approach is demonstrably more effective for the modern business. Let’s explore some of the effects that a proactive and reactive strategy can each have on your operations.
We typically use this blog to share information about the technology that a business should be leveraging - but in this blog, we’ve decided to focus on a different group that is increasingly reliant on technology: students. As these pupils will someday make up the workforce and almost certainly utilize technology on a daily basis, it is important that their education reflects this increase in their curriculums. Here, we’ll consider some of the effects (good and bad) that this has had.
Let me ask you a simple question: how many cell phones have you had over the years? For some of us, upgrades are a yearly occurrence. For others possibly bi-yearly. Have you ever wondered where your old cell phone goes after it is out of your hands?
Budgeting for your technology can be pretty difficult. You never really know when some problem is going to present itself and cost your business an arm and a leg. Since you can’t always see what’s coming, saving money when you can is important. Let’s take a look at a few ways that you can save money on your business’ IT.
When thinking about securing your business from cyber threats, the mind quickly turns to phishing, hacks and viruses, but there are many security threats in and around the office that can expose your business to a host of threats and cybersecurity issues. In conjunction with a solid cybersecurity solution provided by your MSP, be sure you and your employees follow these office tips to protect your physical workspace from system comprises, unauthorized breaches and data loss.
It’s difficult to put a value on your organization’s technology solutions. While you might be tempted to assign a monetary value based on how much it all saves you, you also need to examine how much it costs you in the long term. Can you optimize your network even more than it currently is? Can you even keep track of the countless moving parts of your IT infrastructure? Managed IT might be able to help.
Windows is a great operating system, but unless you’re keeping track of which version you have, you’ll be in for a rude awakening when it comes time to upgrade. In just six short months, there will be two Windows End of Life events for major technology solutions: Windows 7 and Windows Server 2008 R2. You need to start thinking about upgrading now before it’s too late to do so.
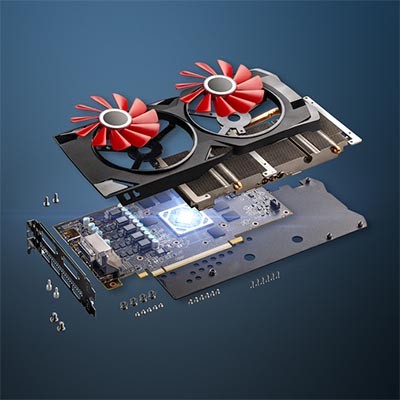
In parts one through four we talked about choosing the right specifications for your desktop, depending on its role. We talked about selecting the right CPU, RAM, storage, and display options. This final post we hit a few other tips and ideas we came up with that didn’t fit into the other posts.
Your new desktop isn’t going to do you much good if you don’t have a screen to plug into it. Let’s talk about considerations to make when purchasing a new desktop when it comes to your display.
Small and medium-sized businesses (SMB) have historically been restricted in what they can do with their technology infrastructures. However, there are now options that an SMB can leverage that enable it to accomplish more with their infrastructure - but this requires the SMB to have a plan in place.
The cloud can bring numerous benefits to a business. Public cloud offerings can reduce technology costs, provide scalability and flexibility to a business’ computing infrastructure, promote collaboration, protect your business from data loss, and much, much more. What it cannot do, however, is guarantee the control some organizations wish to have over their technology infrastructure. Some businesses prioritize that control, while others are bound by industry and government-induced regulations. For those businesses, there is the hybrid cloud.
Let me ask you a question… let’s say that you’re about one year from your projected retirement, when a ransomware attack encrypts all of your files. What do you do? Pack it in and retire early? This is precisely the situation that the practitioners of Brookside ENT & Hearing Services of Battle Creek, Michigan, have found themselves in - and it may not be over yet.
Manufacturing products is still a major part of the western economies; and, like other businesses, manufacturers are using information technology to fuel and manage their supply chains and business processes. We’ll take a short look at what IT manufacturers use, and how it helps them forge their business ahead.
Microsoft Word’s massive cache of options and its relative ease of use are two of its defining characteristics. This presents organizations and users alike with a large set of different ways they can set up the word processor. Today, we will take you through Word, providing tips on how to change these settings so that you can get the most out of it.
Mobile? Grab this Article!
Tag Cloud